
Lateral motion is a time period that has develop into more and more outstanding inside cybersecurity circles, however is essentially unknown to a basic enterprise viewers. Nevertheless, as we’ll present on this article, business leaders and IT professionals should perceive this time period and its implications for his or her group.
What precisely is lateral motion? Merely put, lateral motion refers back to the strategies cybercriminals use to navigate by a community, transferring from one system to a different looking for invaluable knowledge or property. They do that after gaining preliminary entry, usually by phishing or different deception-based techniques, with the last word aim of escalating their privileges and sustaining a persistent presence throughout the compromised atmosphere.
The hazard of lateral motion lies in its stealthy nature. Cybercriminals can silently infiltrate a community, transferring laterally undetected, and progressively acquire extra affect and management. They will then exploit their newfound management to trigger intensive injury, whether or not or not it’s stealing delicate data, disrupting enterprise operations, or deploying ransomware.
Probably the most vital side of lateral motion is that it exposes the weakest hyperlink in your safety chain. For instance, if even one worker workstation has a weak password, and an attacker manages to compromise it, they’ll use lateral motion to succeed in your CRM or ERP system and compromise that as nicely. So a small, seemingly inconsequential assault can flip right into a disaster.
Lateral motion is a key part in superior persistent threats (APTs) and is usually utilized in large-scale knowledge breaches. For this reason understanding lateral movement is essential for companies trying to defend their digital property and preserve their reputations in an more and more cyber-aware world.
Why Are Companies Weak to Lateral Motion?
More and more Advanced and Interconnected IT Surroundings
We live in an period of digital transformation. Companies throughout all sectors are more and more counting on advanced and interconnected IT infrastructures to assist their operations and drive development. This interconnectivity, whereas helpful for collaboration and effectivity, additionally presents an expanded floor space for potential cyber-attacks.
The complexity of those networks could make it difficult to watch and handle safety successfully. In lots of circumstances, as soon as an attacker positive aspects entry to at least one part of the community, they’ll simply traverse by the interconnected methods undetected. That is the essence of lateral motion, making it a major menace to fashionable companies.
The Problem of Inside Community Monitoring
Monitoring inside community exercise is a frightening job for a lot of companies. The sheer quantity of knowledge generated inside a typical company community may be overwhelming, making it troublesome to determine doubtlessly malicious exercise amidst the noise of legit visitors.
Furthermore, many conventional safety options are targeted on stopping exterior threats and will overlook suspicious exercise occurring throughout the community. This lack of inside visibility can permit cybercriminals to maneuver laterally with out detection, escalating their privileges and compromising crucial methods.
Inadequate Segmentation and Entry Controls
Segmentation means dividing a community into separate, remoted sub-networks. In an ideally segmented community, methods and sources are separated into distinct zones, with strict entry controls regulating visitors between these zones.
Nevertheless, in lots of companies, inside segmentation is usually neglected or poorly carried out. This could permit an attacker who has infiltrated one space of the community to simply transfer to others. Moreover, insufficient entry controls can allow cybercriminals to escalate their privileges and entry delicate sources, exacerbating the potential injury brought on by a breach.
How Lateral Motion Works: Widespread Risk Vectors
Credential Theft
The primary menace vector we’ll look at is credential theft. Credential theft is a harmful and in style methodology used to facilitate lateral motion inside a community. As soon as inside, attackers might goal administrative accounts or customers with elevated privileges to realize entry to delicate data and management over crucial methods.
The method usually begins with a profitable phishing assault, the place an unsuspecting person is tricked into revealing their login particulars. As soon as the attacker has these credentials, they’ll authenticate themselves throughout the community and start to maneuver laterally. They could additionally search to escalate their privileges, usually by exploiting system vulnerabilities, to entry much more delicate data.
Credential theft isn’t simply restricted to passwords. Attackers may steal digital certificates, SSH keys, and different types of authentication tokens. These can then be used to impersonate legit customers or companies throughout the community, additional facilitating lateral motion. As a result of these assaults usually mimic legit person conduct, they are often troublesome to detect with out the best monitoring and safety instruments in place.
Distant Execution Instruments
One other frequent technique of facilitating lateral motion is thru using distant execution instruments. These instruments permit attackers to execute instructions or deploy malware on distant methods throughout the community.
One in style methodology is thru using PowerShell, a strong scripting language and shell framework utilized by Home windows directors for job automation and configuration administration. PowerShell scripts can be utilized to execute instructions on distant methods, collect data, and even deploy malware. As a result of PowerShell is a legit instrument utilized by directors, its use by attackers can usually go unnoticed.
The hazard with distant execution instruments is that they permit attackers to succeed in methods that may in any other case be inaccessible. They will also be used to automate the lateral motion course of, permitting attackers to rapidly and effectively transfer by a community.
Software and Service Exploitation
The third menace vector we’ll take a look at is software and repair exploitation. This entails the abuse of legit functions and companies to facilitate lateral motion.
As an illustration, an attacker may exploit a vulnerability in an online software to realize preliminary entry to a community. From there, they could hunt down different susceptible functions or companies to use, permitting them to maneuver laterally throughout the community.
One of these assault is especially harmful as a result of it may possibly usually bypass conventional safety measures. Firewalls and intrusion detection methods might not choose up on this kind of exercise as a result of it seems to be legit visitors.
Along with exploiting vulnerabilities, attackers may abuse legit options of functions and companies to facilitate lateral motion. For instance, they could use the distant desktop protocol (RDP) to maneuver from one system to a different, or they could use the file switch capabilities of an FTP server to maneuver malware or stolen knowledge throughout the community.
Session Hijacking
Session hijacking is one other frequent methodology used to facilitate lateral motion. This entails the interception and abuse of community classes to realize unauthorized entry to methods and knowledge.
A typical situation may contain an attacker who has gained entry to a community sniffing the community visitors to determine lively classes. As soon as they’ve recognized a session, they’ll then try to hijack it, both by injecting malicious knowledge into the session or by taking on the session fully.
Session hijacking may be notably troublesome to detect as a result of it usually entails the abuse of legit classes. Until the hijacked session displays uncommon conduct, it might go unnoticed by community safety instruments.
Insider Threats
The ultimate menace vector we’ll focus on is insider threats. This entails the abuse of licensed entry by somebody throughout the group to facilitate lateral motion.
Insider threats can take many types. It would contain a disgruntled worker in search of to trigger hurt, or it’d contain an worker who has been tricked or coerced into aiding an attacker.
One of many causes insider threats are so harmful is as a result of they usually contain customers with legit entry to methods and knowledge. This could make it tougher to detect and stop insider threats, particularly if the person is cautious to keep away from elevating any pink flags.
Lateral Motion: Prevention and Mitigation Methods
Listed here are just a few steps companies can take to stop the specter of lateral motion, and keep away from minor assaults from escalating into main breaches.
1. Implementing Sturdy Entry Controls and Person Privileges
One of the efficient methods to stop lateral motion is by implementing sturdy entry controls and person privileges. This entails rigorously managing who has entry to what data and methods inside your community, in addition to what they’re allowed to do with that entry. This not solely reduces the chance of an attacker gaining entry within the first place, but in addition limits the injury they’ll do in the event that they do handle to breach your defenses.
This technique requires you to have understanding of your community and the roles of the individuals who use it. It’s best to know who wants entry to what, and why. With this data, you’ll be able to then arrange controls that give every person the entry they should do their job, and nothing extra. This precept is named ‘least privilege,’ and it’s a basic a part of good cybersecurity.
2. Implementing Community Segmentation
One other efficient technique for stopping lateral motion is inside community segmentation. This entails dividing your community into separate segments, every of which is strongly remoted from the others. Because of this even when a hacker manages to infiltrate one phase of your community, they received’t mechanically have entry to the others.
Community segmentation may be achieved in varied methods, reminiscent of by using firewalls, Digital Native Space Networks (VLANs), or different community units. The bottom line is to make sure that every phase is successfully remoted from the others, stopping any unauthorized motion between them.
3. Common Patching and Updates
Maintaining your methods and software program updated is one other essential technique for stopping lateral motion. It is because many cyberattacks exploit recognized vulnerabilities in outdated software program. By commonly patching and updating your methods, you’ll be able to make sure that these vulnerabilities are mounted, making it a lot more durable for an attacker to realize entry.
This technique requires a proactive method to system upkeep. You must keep knowledgeable about any new patches or updates which are launched to your software program and implement them as quickly as potential. This is usually a time-consuming job, nevertheless it’s nicely definitely worth the effort when you think about the potential value of a profitable cyberattack.
4. Multi-Issue Authentication
Multi-factor authentication (MFA) is one other efficient instrument within the combat in opposition to lateral motion. MFA requires customers to supply two or extra items of proof to substantiate their identification earlier than they’ll entry a system. This could possibly be one thing they know (like a password), one thing they’ve (like a bodily token), or one thing they’re (like a fingerprint).
By requiring a number of items of proof, MFA makes it a lot more durable for a hacker to realize entry to your methods. Even when they handle to steal or guess one piece of proof (like a password), they are going to nonetheless be unable to realize entry with out the others. This considerably reduces the chance of lateral motion inside your community.
5. Behavioral Analytics and Anomaly Detection
Lastly, behavioral analytics and anomaly detection also can play a key function in stopping lateral motion. These strategies contain monitoring the exercise in your community and on the lookout for something uncommon. This could possibly be something from an sudden login try to a sudden spike in community visitors.
By detecting these anomalies, you’ll be able to doubtlessly spot a cyberattack in its early phases, earlier than any vital injury has been completed. This provides you the possibility to reply rapidly and successfully, minimizing the affect of the assault and stopping additional lateral motion inside your community.
Conclusion
In conclusion, whereas lateral motion is a major menace to cybersecurity, there are various methods that can be utilized to stop and mitigate it. By implementing sturdy entry controls, segmenting your community, protecting your methods up to date, utilizing multi-factor authentication, and monitoring for anomalies, you’ll be able to considerably scale back the chance of lateral motion inside your community. Nevertheless, it’s necessary to keep in mind that no single technique is foolproof. The simplest method is to make use of a mix of methods, creating a sturdy, multi-layered protection in opposition to cyber threats.
Featured Picture Credit score: Offered by the Writer; Thanks!
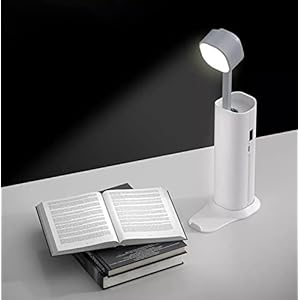
Trending Merchandise



![CRATIX 360°Rotatable and Retractable Car Phone Holder, Rearview Mirror Phone Holder [Upgraded] Universal Phone Mount for Car Adjustable Rear View Mirror Car Mount for All Smartphones](https://m.media-amazon.com/images/I/410N7NZtIjL._SS300_.jpg)




![Car Phone Holder Mount, [Military-Grade Suction & Super Sturdy Base] Universal Phone Mount for Car Dashboard Windshield Air Vent Hands Free Car Phone Mount for iPhone Android All Smartphones](https://m.media-amazon.com/images/I/51KK2oa9LDL._SS300_.jpg)
